Points to note after endpoint configuration
Incorrectly configured endpoints may cause unexpected data leaks. Below are some precautions to take after setting up endpoints so as to keep your site secure.
Managing unused columns with the post-processing allow function
By default, all columns are published. To publish only specified columns, use the post-processing allow function.
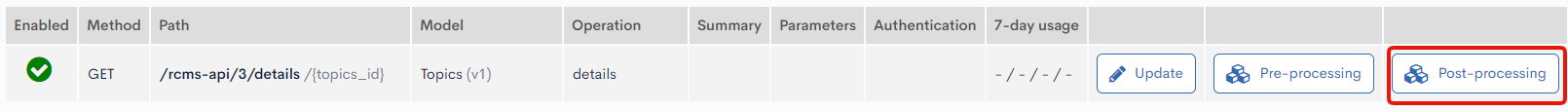
Navigate to the endpoint list screen. Click [Post-processing] next to the target endpoint, and select [Add] -> [Allow list].
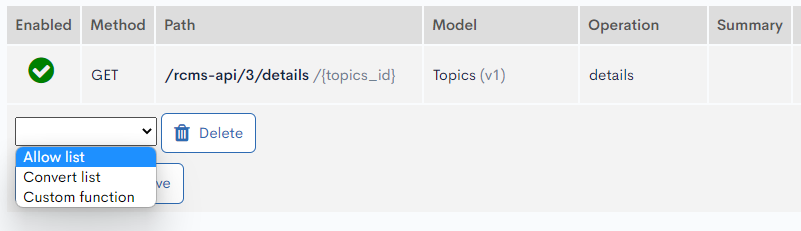
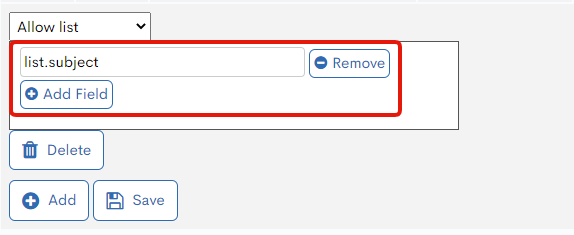
Add the fields to be included in the allow list and click [Save] when you are done.
For more information on endpoint post-processing settings, see User guide: API post-processing.
Verifying CORS configuration
On the endpoint list screen, click [Operation CORS] to view your CORS settings.
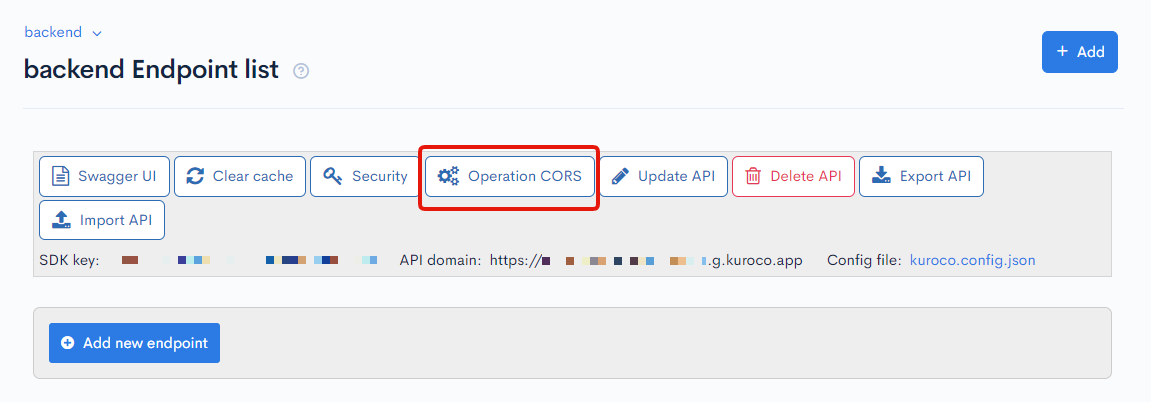
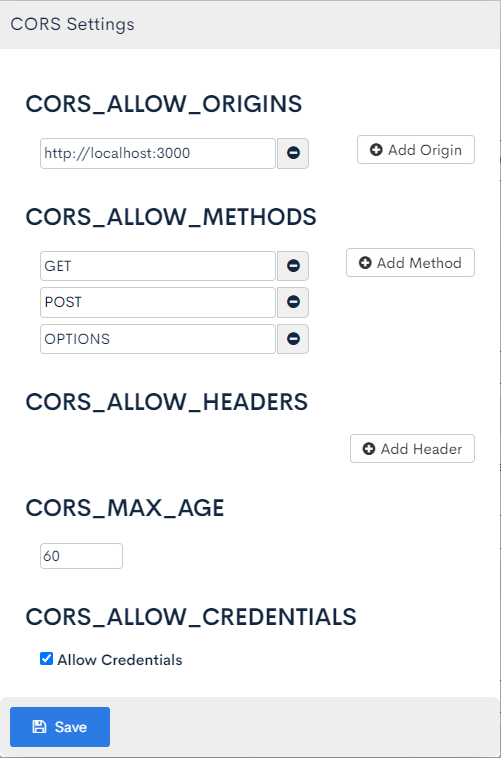
Make sure to remove any test URLs entered under "CORS_ALLOW_ORIGINS" when your site is published.
For more information on CORS settings, see User guide: API - Operation CORS.
Verifying API security
Click [Security] on the endpoint list screen to configure your API security options.
You can set up IP address restrictions to allow access only from specified IP addresses.
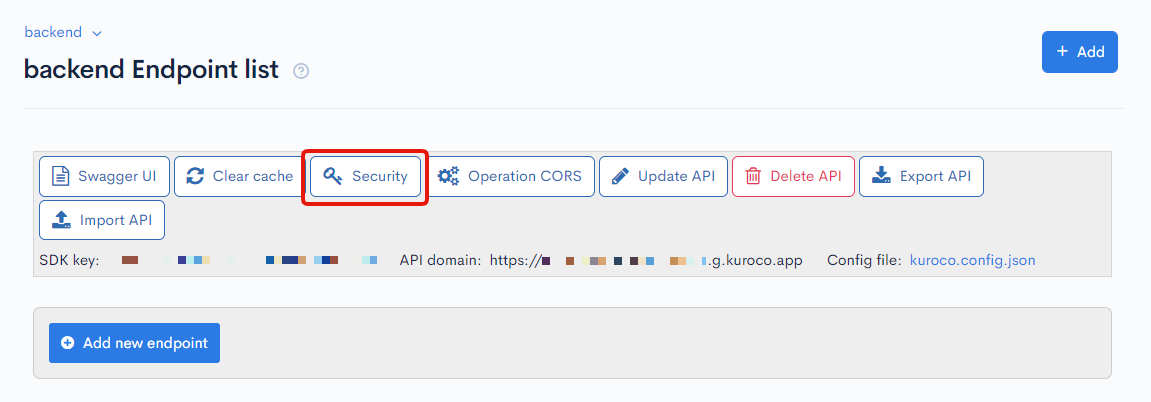
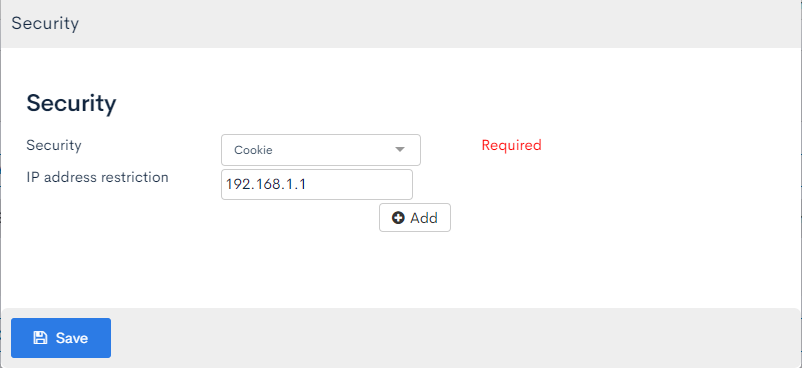
For more information on API security settings, see User guide: API security.
Verifying endpoint API request restriction
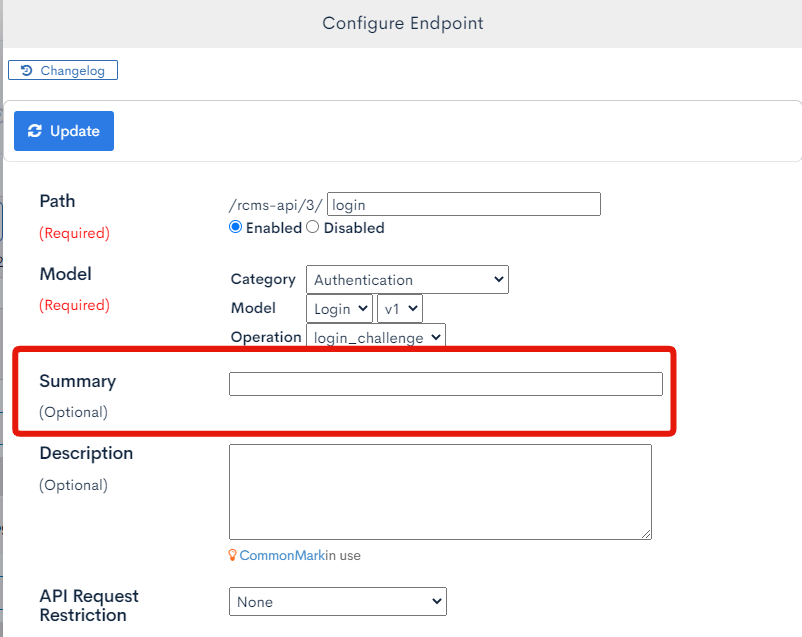
The "Configure endpoint" dialog enables you to set and verify API request restriction.
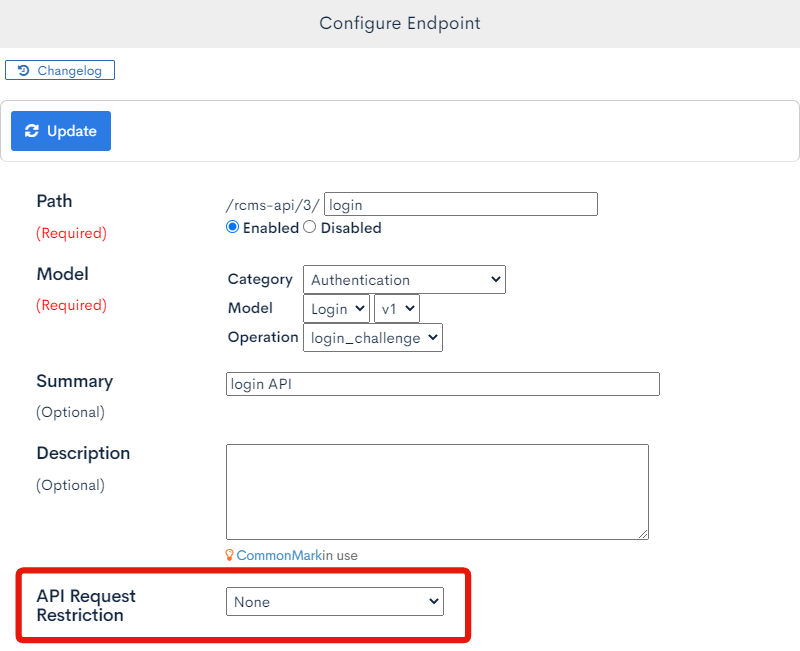
Select one of three API request restriction options:
- None
- GroupAuth
- MemberCustomSearchAuth
The [GroupAuth] and [MemberCustomSearchAuth] options verify user privileges when using the API, and requests are approved only if user permissions match the specified settings.
Removing unused endpoints
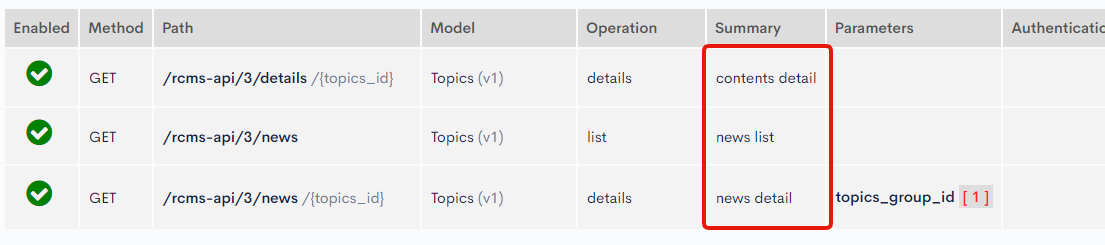
You should delete unused endpoints or include a summary for them in the settings dialog. To facilitate operations, clearly state the purpose of the endpoint in the summary.
Saved summaries are displayed on the endpoint list screen.
Support
If you have any other questions, please contact us or check out Our Slack Community.